AES 256 Encryption. Why You Should Use it?

In today’s digital world, data breaches and cyberattacks are more common than ever. Even ordinary people have to care about the security of their data. But have you ever wondered how nuclear weapon codes, bank accounts, and top-secret government information are secured? The answer lies in military-grade encryption, and one of the most trusted algorithms is AES-256 encryption.
The good news? AES 256 is not just for governments – it’s a public standard that anyone can use to protect sensitive files, operating systems, and firmware. In this article, we’ll explain what AES 256 is, how it works, and why it’s essential for individuals and organizations looking to secure their data.
What Is AES 256 Encryption?
Advanced Encryption Standard (AES) 256 is a symmetric encryption algorithm that uses a 256-bit key to convert readable data (plain text) into secure, unreadable ciphertext.
Put simply, AES 256 makes your information unreadable without the proper decryption key. Unlike simple password protection, AES 256 is designed to withstand even the most sophisticated hacking attempts.
How AES 256 Encryption Works
To understand AES 256, it helps to know the basics of encryption. Encryption transforms readable data into ciphertext, which is unreadable to humans and computers without the correct key.
AES 256 takes this process several steps further, making it one of the most secure algorithms available:
How AES Breaks Your Data Into Manageable Blocks
AES processes data in 128-bit blocks, arranging them in 4×4 arrays of bytes. This block-based system allows AES to handle large volumes of data efficiently and securely.
Generating Multiple Encryption Keys for Maximum Security
AES 256 doesn’t just use the original key; it generates multiple round keys through Rijndael’s key schedule, ensuring that every encryption cycle is unique and harder to crack.
Incorporating the Round Key to Scramble Data
The algorithm adds the first round key to your data, immediately scrambling the content and starting the encryption process.
Replacing Bytes for Stronger Encryption
Each byte in the 4×4 array is substituted with another byte using a fixed substitution table (S-box). This step adds complexity to the encryption and makes patterns nearly impossible to detect.
Rearranging Data Rows for Added Complexity
AES then shifts rows in the array left by varying amounts. This rearrangement ensures that data is evenly spread across the block, further complicating decryption attempts.
Combining Columns to Strengthen Diffusion
Columns of data are mathematically combined using a pre-defined matrix, a process known as mixing columns. This increases diffusion, meaning small changes in input affect the entire output, making brute-force attacks nearly futile.
Repeating Encryption Cycles to Boost Security
AES 256 repeats these steps 14 times, adding new round keys each time. Multiple encryption rounds make AES 256 extremely resistant to brute-force and cryptanalytic attacks.
Why AES 256 Is Special
AES 256 isn’t just another encryption algorithm; it’s the gold standard in cybersecurity. Here’s why you should use it:
Virtually Unbreakable
While theoretically possible, AES 256 would take billions of years to crack using brute-force attacks – even with the most powerful computers. Keeping your encryption keys private ensures your sensitive data remains secure for decades.
Symmetric Key Encryption Offers Speed and Efficiency
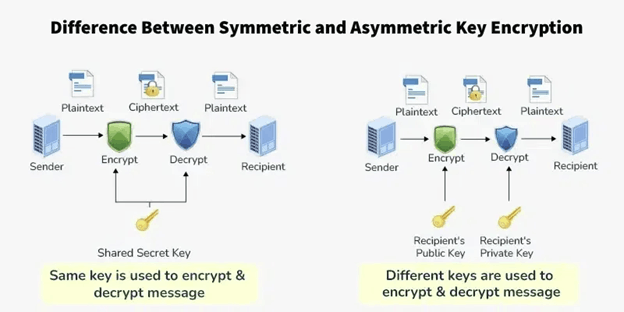
AES 256 uses a single symmetric key for both encryption and decryption. Symmetric encryption offers several advantages:
- Faster processing speed
- Ideal for internal organizational data
- Efficient for encrypting large volumes of data
- Requires less computational power than asymmetric encryption
Although asymmetric encryption also has its use cases, AES 256 is currently the most capable symmetric encryption method available.
Preventing Security Breaches From Turning Into Data Breaches
Even if hackers penetrate your systems, AES 256 ensures that stolen data remains encrypted and useless. This helps prevent:
- Compliance violations
- Identity theft
- Ransomware attacks
Statistics indicate that 60% of small businesses fail within six months of a cyberattack, but AES 256 reduces the likelihood of a security incident escalating into catastrophic data loss.
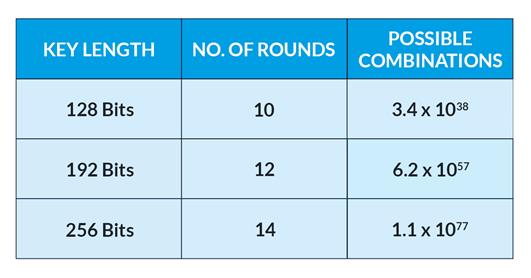
Future-Proof Security With the Strongest AES Layer
AES comes in three key sizes: 128-bit, 192-bit, and 256-bit. While AES 128 is still strong, AES 256 provides quantum-resistant security, making it the most future-proof encryption layer against emerging threats from quantum computing.
How Hard Is It for Hackers to Break AES 256?
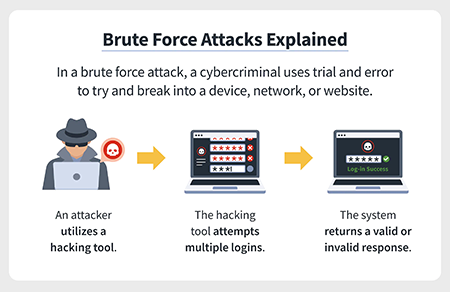
To decrypt AES 256, a hacker would need to try 2^256 combinations – more than the number of atoms in the observable universe. Even if someone attempted this, the computational power required simply doesn’t exist yet.
AES 256 is practically unbreakable, offering unmatched security for sensitive personal and organizational data.
Why AES Alone Isn’t Enough

AES 256 encryption is powerful, but encryption cannot exist in isolation. Hackers can still attempt to:
- Steal cryptographic keys
- Exploit side-channel attacks
- Access data before or after encryption
For complete protection, AES 256 should be integrated with a Managed File Transfer (MFT) system.
Enhancing AES 256 With Managed File Transfer (MFT)
Pairing AES 256 encryption with MFT creates a robust data security ecosystem. MFT ensures your encryption keys and files remain protected by offering:
- Strict access controls to prevent unauthorized use of cryptographic keys
- Multi-Factor Authentication (MFA) to secure AES infrastructure
- Real-time reporting on file access and transfers
Combining AES 256 and MFT protects data both in transit and at rest, creating a comprehensive, end-to-end security solution.
Solutions like MOVEit integrate AES 256 with MFA, strict access controls, and secure file transfer, making them ideal for organizations that require compliance-ready, secure data infrastructure.
Key Takeaways
- AES 256 encryption is military-grade and future-proof, offering the highest level of symmetric key security.
- It prevents security breaches from turning into catastrophic data breaches.
- AES 256 is fast, efficient, and ideal for large-scale organizational data.
- Pairing AES 256 with Managed File Transfer (MFT) ensures maximum protection.
If you want to secure your files and prevent cyberattacks, AES 256 encryption is the closest thing to a data security magic wand – but only when combined with proper access controls and infrastructure.